HeapLAB Review - GLIBC Heap Exploitation with Max Kamper
I recently traveled to London to take part in a brand new training course called HeapLAB - GLIBC Heap Exploitation with Max Kamper. While Max's name might not stand out to you, his body of work almost certainly will. He is the creator of ROPEmporium, a hugely popular (at least amongst my friends) website focused on teaching x86 Return-Oriented Programming exploitation techniques. To be completely honest, he's a bit of a celebrity in my eyes so I jumped at the chance to take his new in-person course.
 |
| Max Kamper |
When arriving at the training, Max will give you a USB-A drive containing an lubuntu VM and a Heap Exploitation Bible document. As the name of the course suggests, the VM contains a number of different binaries, all designed to teach you different heap exploitation techniques.
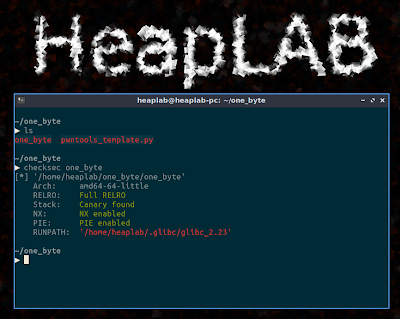
I think Max did a great job thinking through how folks taking his course would best consume the content. The HeapLAB VM is setup with everything ready to go. No additional configurations are needed. You just hop into the directory for the technique Max is teaching and you have everything you need - pwnable binaries, templated exploit code and solution dot files.
Much like with the ROPEmporium challenges, each binary you interact with throughout the course requires minimal, if any, reversing. The bugs themselves, such as a double free or write-after-free, will be immediately apparent when using the binary. I think this is one of the training's strong points - it removes a lot of the peripheral tasks and keeps you focused on the technique at hand which are complicated enough on their own.
As to the techniques themselves, with rare exception, such as the unsafe unlink, these techniques are applicable to glibc versions found on most modern linux systems. We spent most of our time on very recent versions of glibc, including 2.27 which is included with ubuntu 18.04 LTS.
Additionally, I really appreciated the effort Max took to make the binaries as realistic as possible. Each binary only contains one bug. At no point in the training is Max teaching some contrived scenario where 3 or 4 bugs have to line up in a certain way. In fact, the very first challenge binary you get at the end of day 1 gives you a single byte heap-based buffer overflow, it has no leaks and has modern memory protections enabled.
While each day of the two day course was supposed to run until about 5pm, we ended up working until about 8pm each night making for 11 hour days, which was only possible because Max was willing to stay and work with us on the various challenge binaries.
Much like with the ROPEmporium challenges, each binary you interact with throughout the course requires minimal, if any, reversing. The bugs themselves, such as a double free or write-after-free, will be immediately apparent when using the binary. I think this is one of the training's strong points - it removes a lot of the peripheral tasks and keeps you focused on the technique at hand which are complicated enough on their own.
As to the techniques themselves, with rare exception, such as the unsafe unlink, these techniques are applicable to glibc versions found on most modern linux systems. We spent most of our time on very recent versions of glibc, including 2.27 which is included with ubuntu 18.04 LTS.
Additionally, I really appreciated the effort Max took to make the binaries as realistic as possible. Each binary only contains one bug. At no point in the training is Max teaching some contrived scenario where 3 or 4 bugs have to line up in a certain way. In fact, the very first challenge binary you get at the end of day 1 gives you a single byte heap-based buffer overflow, it has no leaks and has modern memory protections enabled.
While each day of the two day course was supposed to run until about 5pm, we ended up working until about 8pm each night making for 11 hour days, which was only possible because Max was willing to stay and work with us on the various challenge binaries.
If you want a preview of the course, 44Con posted a teaser video that goes through the house of force and fastbin dup techniques. You can also get a feel for how fast the course moves, which is crazy fast.
Overall, I really enjoyed the course material and how the information was presented. If you're well versed in stack-based exploits, this is a really good course to move you into something pretty different and more applicable to modern binaries. I think the next chance to participate in this training is when it is held at ringzero in August and is something that I would highly recommend taking.
Update: June, 2020
Max has posted the first day of the course online at udemy. This link uses Max's referral code so if you sign up using that link, as I understand it anyway, it's more beneficial to him.
Overall, I really enjoyed the course material and how the information was presented. If you're well versed in stack-based exploits, this is a really good course to move you into something pretty different and more applicable to modern binaries. I think the next chance to participate in this training is when it is held at ringzero in August and is something that I would highly recommend taking.
Update: June, 2020
Max has posted the first day of the course online at udemy. This link uses Max's referral code so if you sign up using that link, as I understand it anyway, it's more beneficial to him.